
Warning
You should never try to interfere with someone else’s system, illegally. Most likely, you will be caught. Getting into a system is the easy part! Bypassing IDS/IPS and the various alerting is where greater skill comes in to play. Everything has vulnerabilities, everything!
When you are caught, you will be prosecuted. Even if you “win” the court battle, you’ll be out the attorney fees and garbage fines that they will throw at you. Hack your own systems only OR get it in writing from your client that you will be doing a penetration test and let them know what that involves. We are not advocating that you use any technique we publish now or in the future to any illegal purpose.
Learn Pen Testing for Free
If you want to learn safely, and legally download MetaSploit, OWASPBWA, DVWA or other systems designed for the purpose of legal pen testing practice. You can even build your own vulnerable system to test various hacks using free versions of VmWare and use the suite of tools from Kali or Back Box, all of which is free.
With that said (now you have no excuse for doing pentests/hacks illegally), don your black hoodie, pour your caffeinated beverage of choice and engage in the following activities when you are legally able to do so using a combination of social engineering and technical prowess to help your clients secure their data using a variation of the PTES technical guideline:
- Pre-engagement Interactions
- what does client want to verify is safe/visible? Figure out what problems you are solving.
- Intelligence Gathering
- gather basic reconnaissance from public and private sources
- Initial Foothold
- social engineering and basic, more intrusive analysis
- Enumerations
- scan and look for vulnerabilities
- Local Privilege Escalation
- access one of the vulnerabilities you found
- Backdoor Persistence
- install rootkits and other persistence vectors
- Domain Privilege Escalation
- look for a domain admin or other higher level account
- Post Exploitation/Data Dumps
- dump domain hashes or other data as per client requests
- Data Identification/Exfiltration
- sort through and make sense of your data grabs
- Reporting
- make the pretty reports that all the clients like
- Burp Suite
- Canvas
- Cobalt Strike
- Core Impact
- Nessus
- Nexpose
Popular Commercial Applications
When you end up working for a red team and get contracts to ethically hack a client’s resources, you will eventually come across the many flavors of commercial tool kits, such as:
To that end, here are a few articles on basic penetration testing techniques that will help with the various steps of white hat, ethical hacking for your clients:
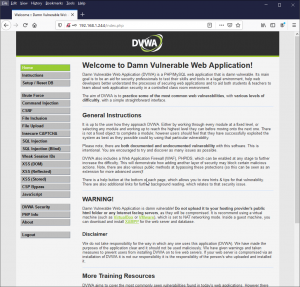
Setup DVWA to Practice Application Security Pentesting
DVWA is a purposefully built “vulnerable” web application designed to teach Application Security pentesting. This guide will show you how to install and configure DVWA. LAMP Stack Base Setup If you haven’t already done so, setup a LAMP stack You will need to remove the default index.html page. Login via SSH and run the following command: Shell sudo rm ...
View HTTP Headers With wget
View http headers with wget to see things like Apache server response codes and more. There are many tools that will allow you to see HTTP headers, such as: curl, fiddler, httpwatch, postman, tcpdump, snoop, and wireshark to name a few. If you don’t have the option to install these, wget ...

Use SSH Tunnel as Socks Proxy Firefox
SSH tunnels are like a poor man’s VPN. You can create an encrypted channel, then pass data over that channel. One of the most common things to pass over an SSH Tunnel is web browsing data (SOCKs Proxy). Basically you will create a SSH Tunnel from your client to a remote server. ...